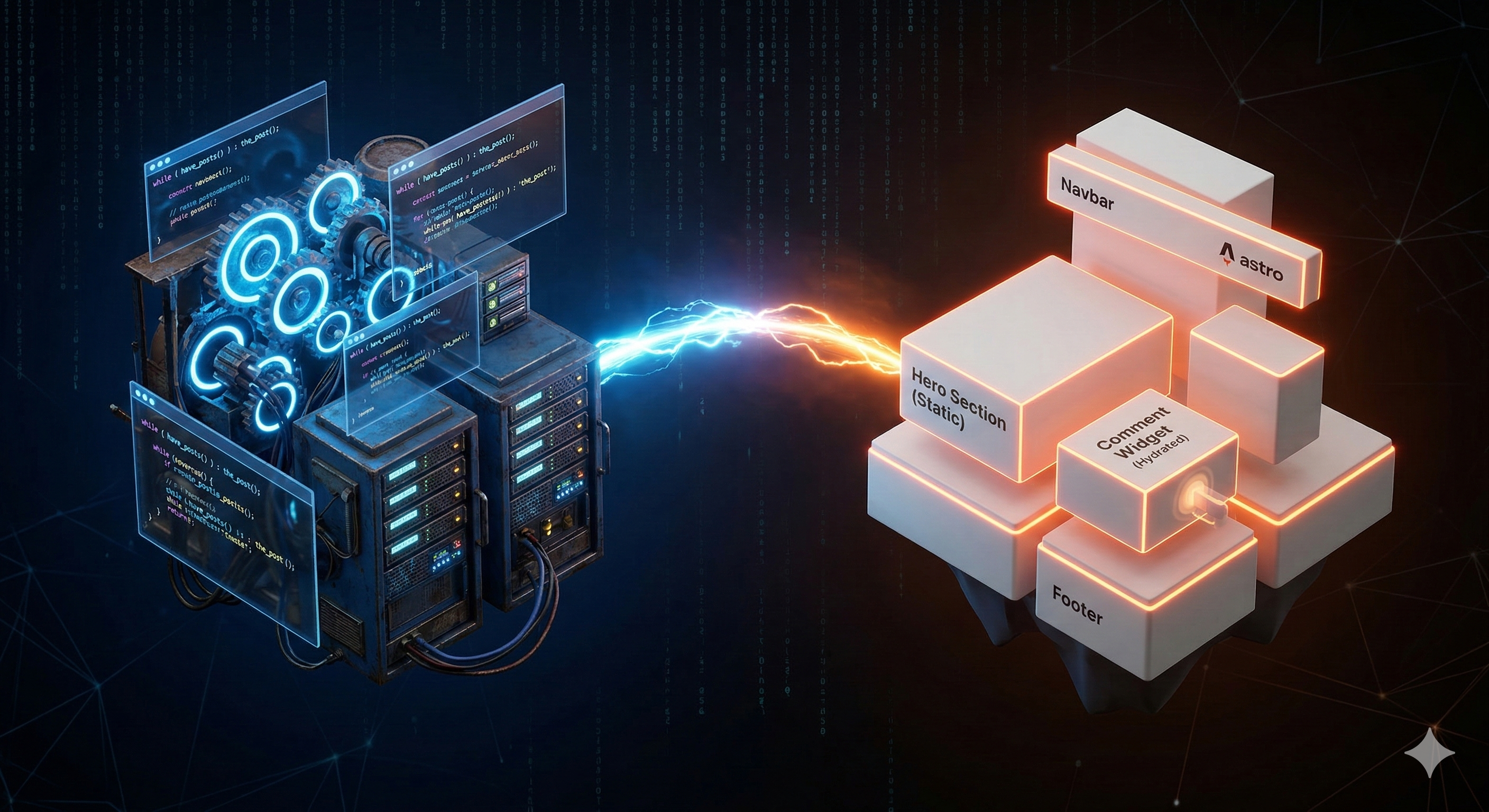
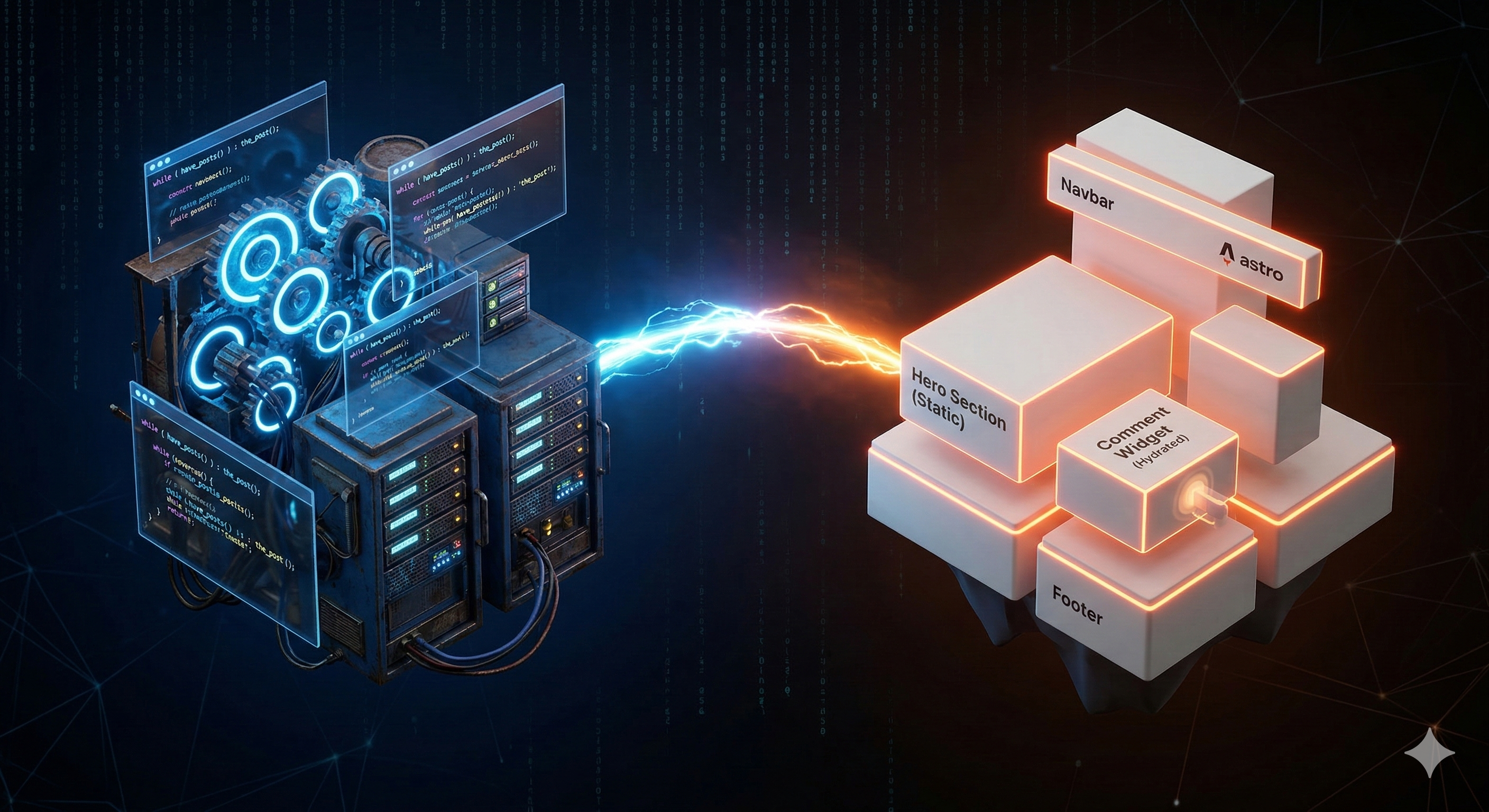
Liberating DomKirby.com From WordPress
Mar 7, 2026
> I’ve been using WordPress since before it had a sidebar. I can’t exactly piece together when I started, but I think it was in 2008 or so. Three different defa...
Read moreThoughts on cybersecurity, technology trends, and the tools that make us more effective.
Mar 7, 2026
> I’ve been using WordPress since before it had a sidebar. I can’t exactly piece together when I started, but I think it was in 2008 or so. Three different defa...
Read more
Dec 23, 2025
It’s hard to believe 2025 is already wrapping. As is pseudo-tradition, I wanted to share a couple of thoughts on how I think 2026 will go and review my original...
Read more
Dec 10, 2025
I figured we would take a little bit of a side quest for a moment on AI. I’ve written a couple of “you’re not AI ready” posts, and I stand by that. However, tha...
Read more
Dec 9, 2025
In my last post, I talked about the “agent hype” we’re all dealing with. The pressure to leverage AI when AI might not be the right solution for the presented p...
Read more
Dec 8, 2025
Click bait title is click bait, but I have a point here. AI is our new obsession, and the current demand is for “agents.” Agents are going to change the world t...
Read more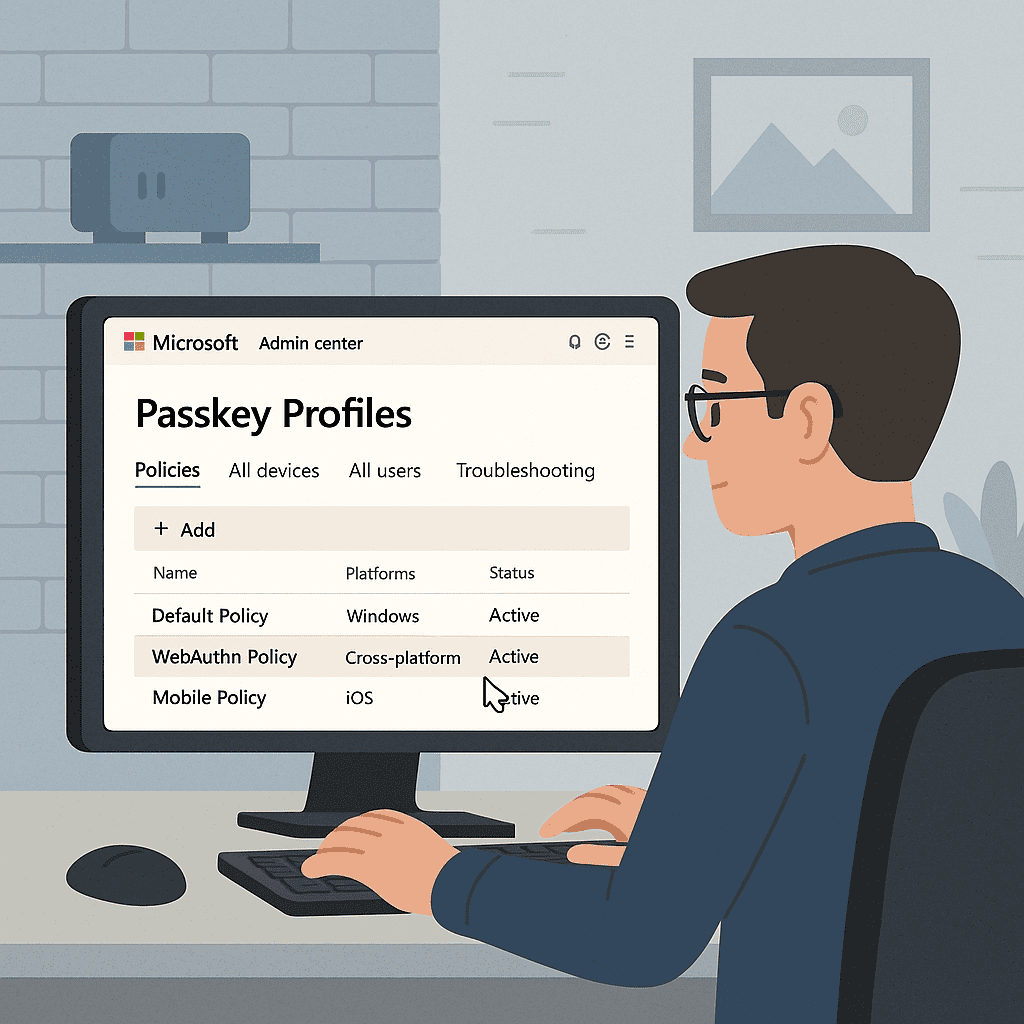
Dec 6, 2025
At Ignite, Microsoft announced that Synced Passkeys would become available in Entra. My initial reaction to this was that it was a terrible idea. However, I've ...
Read more
Oct 2, 2025
In case you don’t know, BitLocker is the disk encryption feature within Windows (including Windows Client and Server). Its job, in a nutshell, is to manage key ...
Read more
Sep 23, 2025
There’s a long-standing debate sort of storming the security community that seems to refuse to die: is Windows Hello, Apple Touch ID, or Android’s credentialing...
Read more
Aug 26, 2025
The almighty tech stack. The best EDR, rock solid email security. “Enterprise technology for the SMB.” I could go on for a while with all the clichés, and I use...
Read more