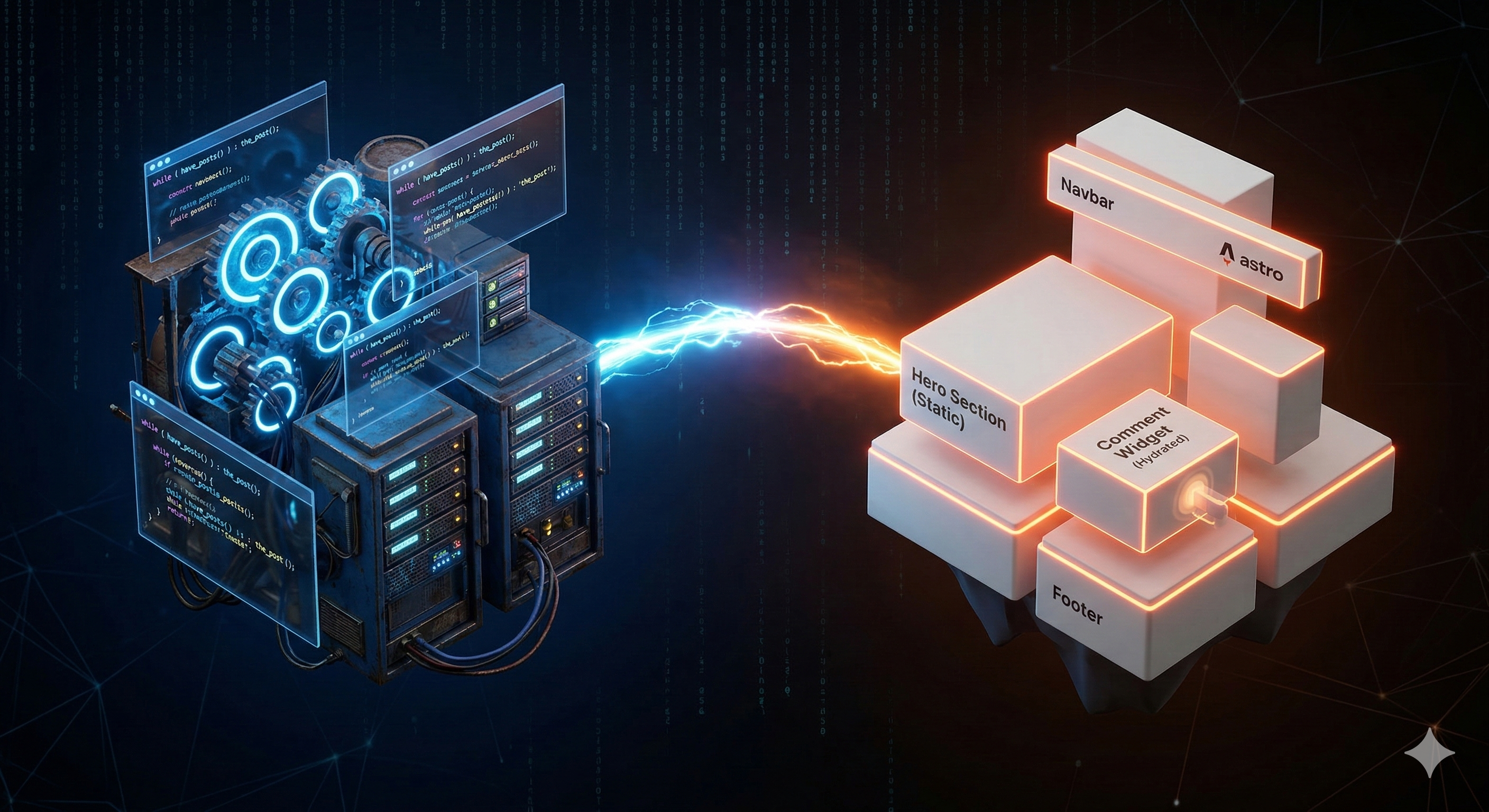
Liberating DomKirby.com From WordPress
Mar 7, 2026
> I’ve been using WordPress since before it had a sidebar. I can’t exactly piece together when I started, but I think it was in 2008 or so. Three different defa...
Read more100 posts
Mar 7, 2026
> I’ve been using WordPress since before it had a sidebar. I can’t exactly piece together when I started, but I think it was in 2008 or so. Three different defa...
Read more
Dec 23, 2025
It’s hard to believe 2025 is already wrapping. As is pseudo-tradition, I wanted to share a couple of thoughts on how I think 2026 will go and review my original...
Read more
Dec 10, 2025
I figured we would take a little bit of a side quest for a moment on AI. I’ve written a couple of “you’re not AI ready” posts, and I stand by that. However, tha...
Read more
Dec 9, 2025
In my last post, I talked about the “agent hype” we’re all dealing with. The pressure to leverage AI when AI might not be the right solution for the presented p...
Read more
Dec 8, 2025
Click bait title is click bait, but I have a point here. AI is our new obsession, and the current demand is for “agents.” Agents are going to change the world t...
Read more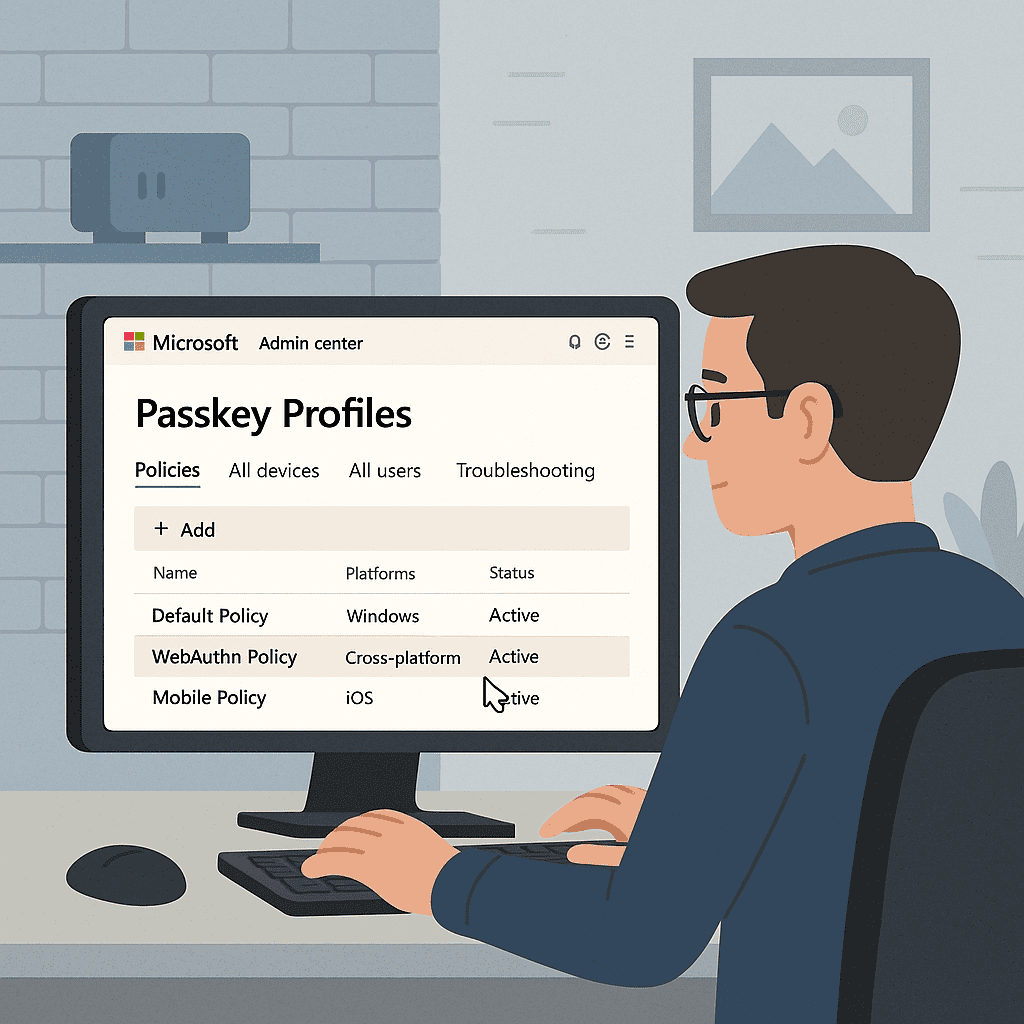
Dec 6, 2025
At Ignite, Microsoft announced that Synced Passkeys would become available in Entra. My initial reaction to this was that it was a terrible idea. However, I've ...
Read more
Oct 2, 2025
In case you don’t know, BitLocker is the disk encryption feature within Windows (including Windows Client and Server). Its job, in a nutshell, is to manage key ...
Read more
Sep 23, 2025
There’s a long-standing debate sort of storming the security community that seems to refuse to die: is Windows Hello, Apple Touch ID, or Android’s credentialing...
Read more
Aug 26, 2025
The almighty tech stack. The best EDR, rock solid email security. “Enterprise technology for the SMB.” I could go on for a while with all the clichés, and I use...
Read more
Jul 19, 2025
I've been a Windows user for as long as I've been a computer user for the most part. I've dabbled in Mac, used plenty of Linux distros. But, day-to-day, I still...
Read more
Mar 4, 2025
Over the weekend (on 3/1 to be exact), there was a significant outage at Microsoft impacting primarily Exchange Online but also some other services. Even though...
Read more
Feb 17, 2025
Device code phishing is a real threat that often goes unmitigated. Microsoft's recent warning that threat actor Storm-2372 is actively executing a device-code p...
Read more
Dec 21, 2024
It's hard to believe that we're closing in on the end of 2024. For me at least, it has been one of those years where being busy keeps the time moving! It's also...
Read more
Nov 26, 2024
One of the only constants in technology is change. Technology advances, we implement new stuff. Or, some sort of upgrade or new version changes the way we do th...
Read more
Nov 25, 2024
Now that Passkeys are generally available, we can start thinking of strategies to implement phishing resistant authentication in our environments! Microsoft has...
Read more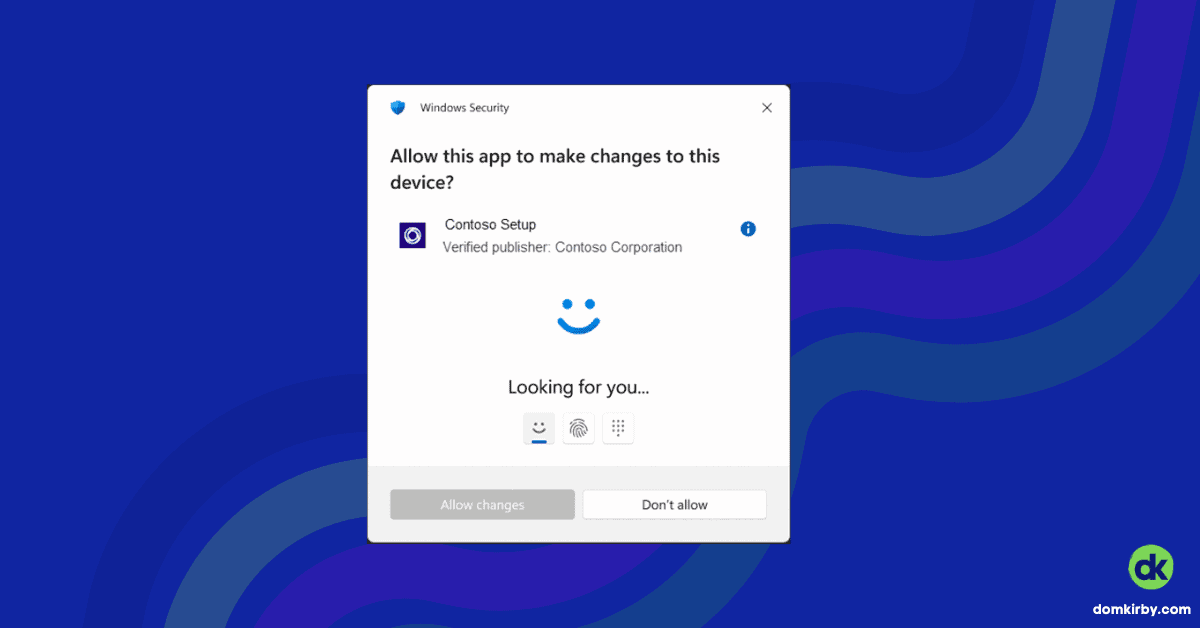
Nov 20, 2024
In another cool Ignite share, Microsoft announced Administrator protection on Windows 11. This feature aims to protect users from malicious code or intent by cr...
Read more
Nov 19, 2024
Awhile back, Microsoft released a preview of soft Passkeys in Microsoft Authenticator. At its core, this feature delivers a cross-device authentication%23) FIDO...
Read more
Sep 8, 2024
We're a little over a month out from Microsoft's upcoming MFA mandate. On October 5th, 2024, the Entra Admin Center, Intune Admin Center, and Azure portal will ...
Read more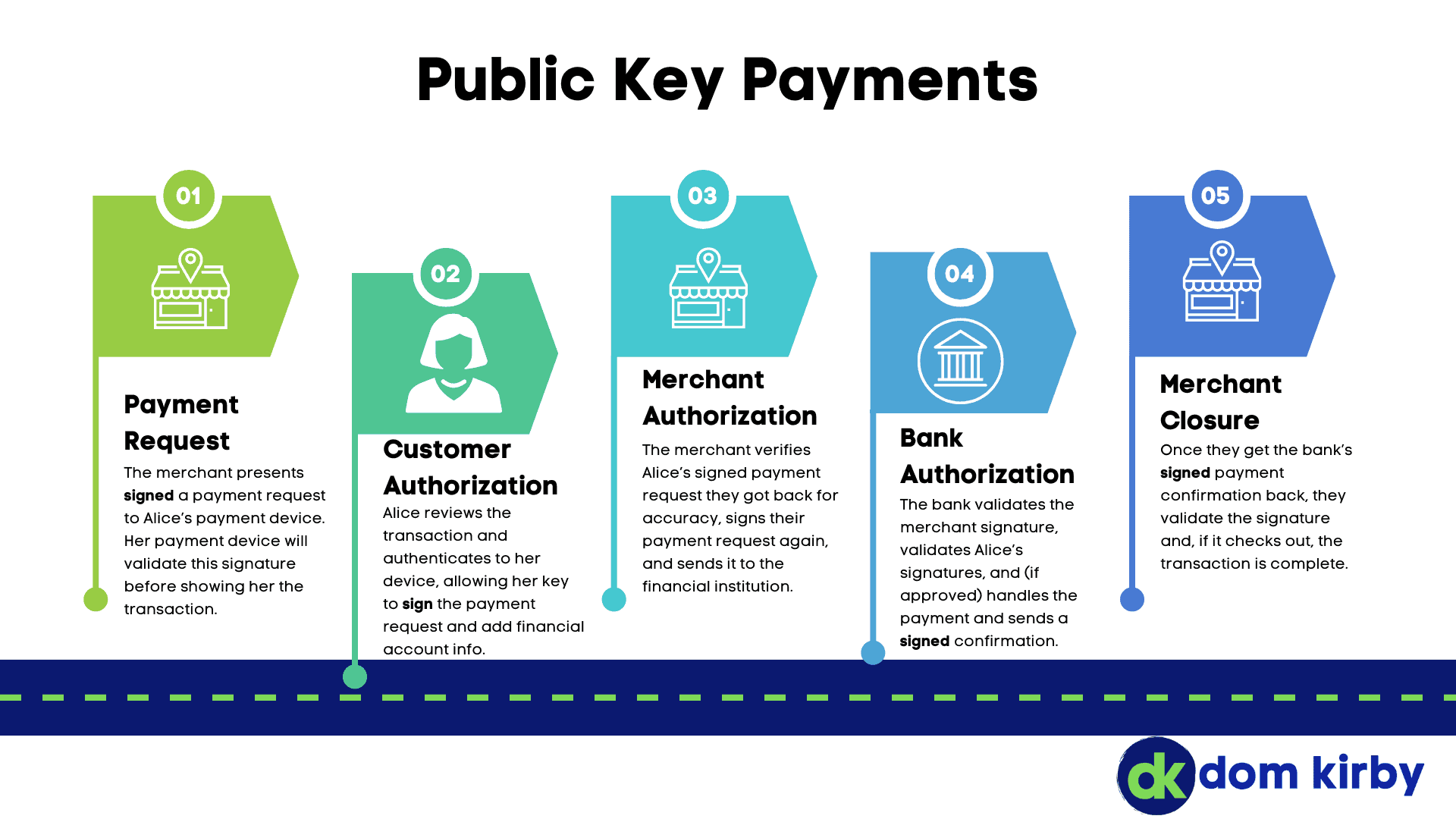
Aug 24, 2024
Payment card fraud is as old as payment cards themselves. First, we used embossed cards and phone calls in the clear to process payments. Then, we had to trust ...
Read more
Jun 17, 2024
I recently came across an article stating that ransomware attacks targeting healthcare organizations surged following the Change Healthcare incident. For a quic...
Read more
Jun 15, 2024
It's time for a new guide for MSPs! The Safeguards within CIS Control 3 speak to the need for proper Data Protection. Implementation Group 1 (i.e.: the minimum ...
Read more
May 9, 2024
In some very exciting news today, CISA announced their Secure by Design Pledge. The Secure by Design Pledge is a voluntary commitment that was signed by 68 soft...
Read more
May 5, 2024
In our digital age, the concept of living in a passwordless world is eagerly anticipated. It's common knowledge that passwords are a hassle – users struggle to ...
Read more
May 4, 2024
IMPORTANT NOTE: I'm trying something new here and looking for feedback (on LinkedIn). I've written this post using Microsoft Copilot by creating a general outli...
Read more
May 3, 2024
If you know me, you know I've been a longtime proponent of Microsoft To Do and its vast integrations across the Microsoft ecosystem. To this day, Microsoft To D...
Read more
Mar 5, 2024
I figured I would expand on my Purview Information Protection information by creating a general guide around information protection labels. In this guide, I tak...
Read more
Mar 4, 2024
I recently made a post on LinkedIn about how I've applied the Traffic Light Protocol within my own Microsoft 365 tenant using Purview Information Protection. I ...
Read more
Feb 26, 2024
In my last post, I wrote about the idea that cybersecurity doesn’t need colleges. For this post, I wanted to shed some light on how I think we can build a moder...
Read more
Feb 25, 2024
It's no secret that we're facing a huge shortage of cybersecurity talent, today and in the future. We are in increasingly desperate need of new blood to fight t...
Read more
Feb 14, 2024
A lot of us, me included, have spelled out some "doom and gloom" about AI and its impact on cybersecurity. Truth is, there's a lot to worry about, especially fo...
Read more
Feb 6, 2024
A lot of folks I work with say that managing remote teams is dramatically different than managing in person teams. In many ways, I agree. However, I also think ...
Read more
Dec 19, 2023
For the first iteration of ‘practically remote,’ I think the topic of “company dynamics” make the most sense. You could also think of it as company structure, b...
Read more
Dec 18, 2023
We’re coming up on 2024, innovation is upon us. Technology enables us to truly make work a thing we do, and not a place we go. Despite the fact that secure and ...
Read more
Dec 12, 2023
I felt like making a fun post and was just recently reminiscing with someone about the joy of getting rid of servers. in my own technology practice, servers wer...
Read more
Nov 29, 2023
In another "real-world impact" story: Hospitals in multiple states are impacted by a ransomware attack against their parent company, Ardent Health. Ardent opera...
Read more
Nov 28, 2023
Two recent incidents have caught my attention, and they're impacting the housing market in a real way at this stage. Mr. Cooper is a loan servicer that claims t...
Read more
Nov 21, 2023
This is an update to my story on the Jeffco Schools incident. Please refer to my "we are human" statement on that post. Defenders: We still see you, and we stil...
Read more
Nov 20, 2023
In my last article, I covered the concerning trend of cyber-attacks aimed at K12 school districts. I've been keeping that up to date as best I can, so check the...
Read more
Nov 8, 2023
\[learn\more caption="Important Preface - We are Human"\] Before we dive in, I want to make something clear. Right now, there are a lot of incident responders d...
Read more
Nov 4, 2023
 Over the last couple of days, Cloudflare suffered a significant outage across its control plane and analytics envir...
Read more
Oct 23, 2023
There seems to be a rather unfortunate crusade against work from home and even hybrid work. There's a number of predicted problems that are driving this type of...
Read more
Sep 11, 2023
Listen, I'm just as excited about artificial intelligence as everyone else. However, like with many things, I am firmly in the camp of "proceed with caution." A...
Read more
Sep 10, 2023
In the first half of 2023, an estimated 39 million people were impacted by 295 data breaches, in the US alone. This is a stupidly staggering number, and it just...
Read more
Jul 27, 2023
Some time ago, I posted about certificate authentication, and certificates themselves. In those articles, I mentioned digital signatures and made a really small...
Read more
Jul 18, 2023
Quite some time ago, I posted about my use of Cloudflare's edge services to protect my WordPress installations. I still use and recommend Cloudflare as a fronte...
Read more
Jun 4, 2023
IaaS (Infrastructure as a Service) might just be the cloud in its purest form. It truly is just "renting someone else's" computer. Because of that, IaaS offers ...
Read more
Apr 20, 2023
If you're a global administrator in a Microsoft tenant, you might have (or soon will) receive an email that reads something like this: > You’re receiving this e...
Read more
Apr 7, 2023
The 3CX incident marked another highly successful supply chain-based attack, believed to be attributable to DPRK (North Korea) state sponsored actors. I won't b...
Read more
Mar 2, 2023
CIS 6.7, CSF PR.AC-1, and just about every other security framework call for centralized account management. SSO is the best way to deliver centralized account ...
Read more
Mar 2, 2023
The White House has unveiled the Biden-Harris Administration National Cybersecurity Strategy, and it has some really important implications for the tech channel...
Read more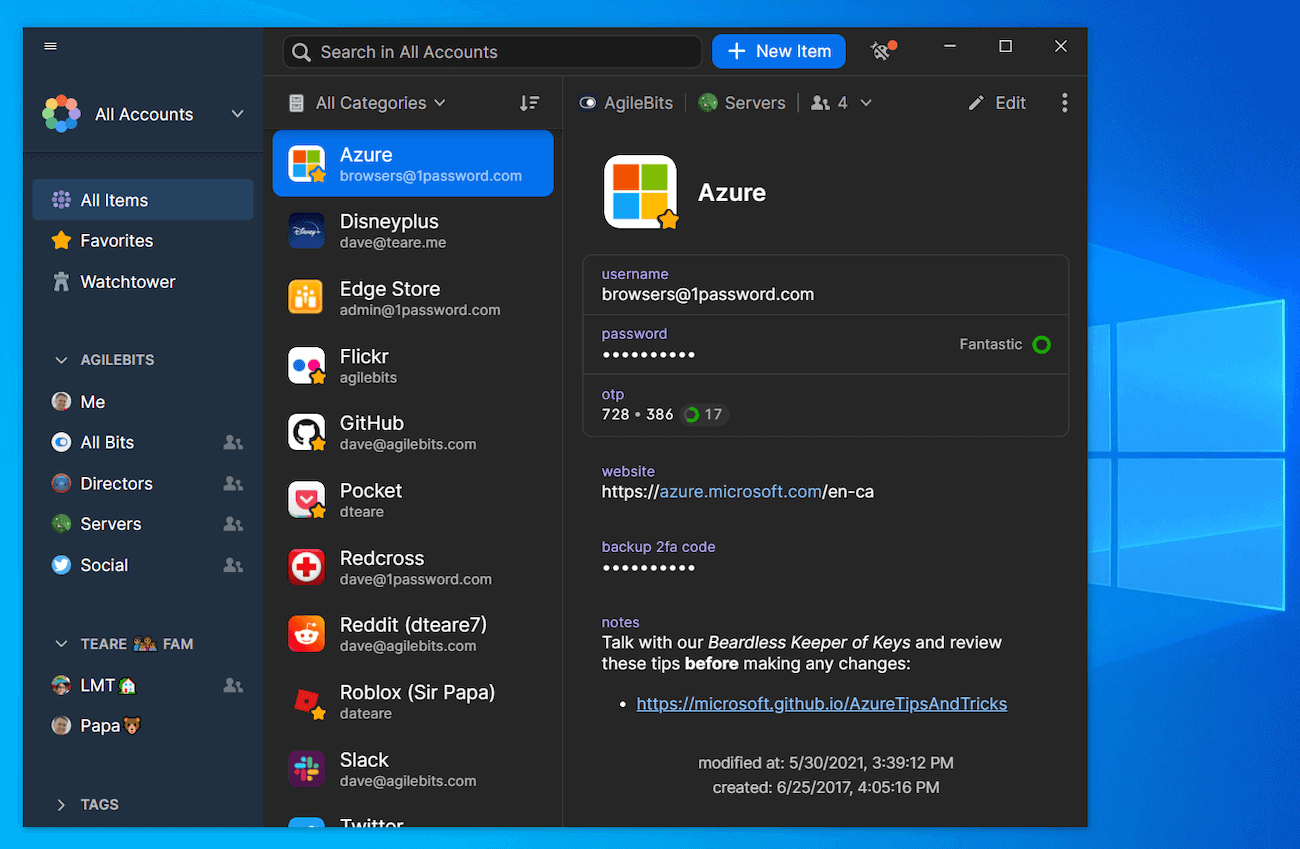
Mar 1, 2023
\[box\] Everyone is responsible for their own security. Me liking a product is not an endorsement of how secure it will be for you. Security is never 100%\[/box...
Read more
Feb 25, 2023
This is a particularly hot topic, and one I'm asked about relatively often. I figured I would cover it here... how do I go about protecting my kids when they're...
Read more
Feb 20, 2023
Today's cybersecurity market is overcrowded, and full of marketing teams who write claims that fall flat on their faces simply in the way they're written. In th...
Read more
Feb 7, 2023
In late January, Microsoft shared that their Microsoft Security has grown to over $20 Billion (USD) in revenue per year. That's a massive milestone and puts the...
Read more
Dec 18, 2022
Has your MSP reached out to tell you that your hardware or software is out of date and you need to buy new stuff? I ran an MSP for five years, and I had to do i...
Read more
Dec 4, 2022
This weekend has been marred by an ongoing outage at major cloud provider Rackspace that is impacting their entire Hosted Exchange offering. After a full day of...
Read more
Nov 27, 2022
Man, I hate printers. But nonetheless, we've got to deal with them. With Basic Authentication finally going away (I hope), you may be running into problems with...
Read more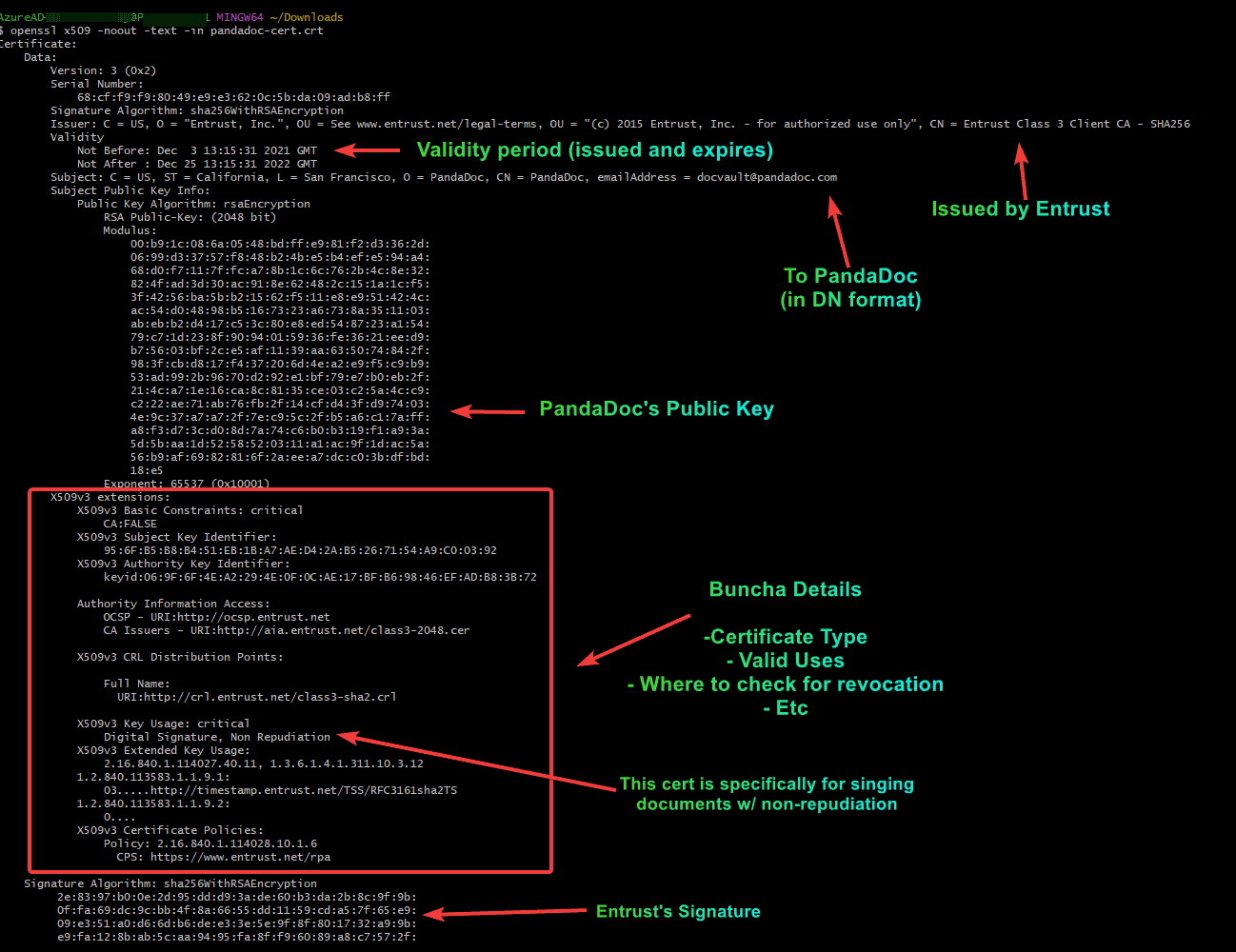
Nov 23, 2022
Following up on my last post about certificate-based authentication, I thought I would break down for the masses what a certificate is exactly. This isn't reall...
Read more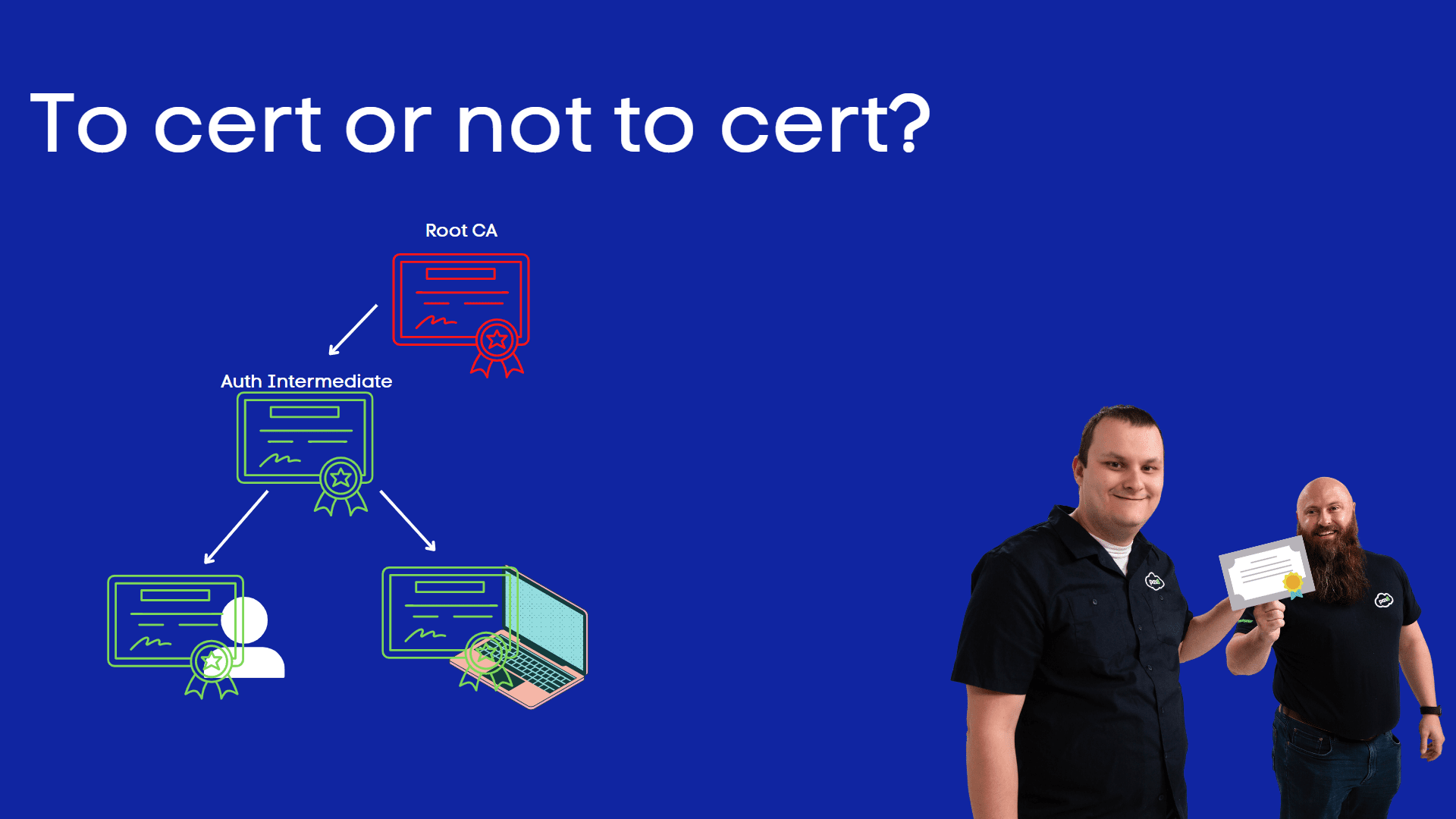
Nov 14, 2022
With Microsoft announcing Certificate Based Auth general availability, it's a fair question. Certificate Authentication is nothing new, native support for CBA i...
Read more
Oct 14, 2022
"Hey Dom, this link looks phishy." I was amazed when somebody actually noticed I was using a custom short linking tool on a social post. To be honest, my first ...
Read more
Oct 10, 2022
It's Cybersecurity Awareness Month, the on month a year where people other than us are paying attention to the details in cybersecurity. Joking aside, public an...
Read more
Oct 1, 2022
Windows 11 22H2 is here, and I think there are some features you should be aware of. These would also be some great noteworthy features to share with your prosp...
Read more
Sep 26, 2022
With the release of Windows 11 22H2, Microsoft has added Enhanced Phishing Protection to its operating system. This feature proactively warns users if they're p...
Read more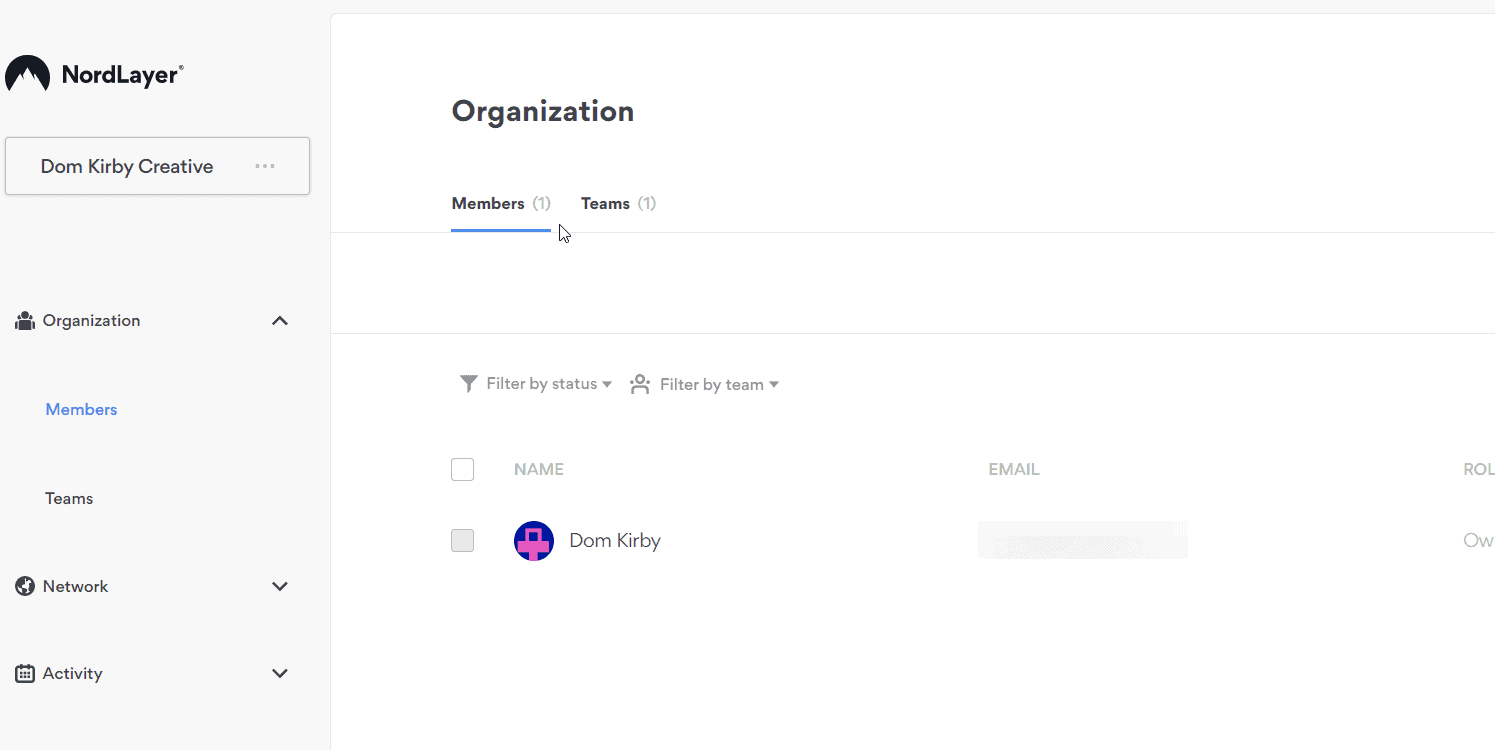
Aug 4, 2022
In July, Pax8 announced a new partnership with Nord Security. I was particularly excited about this launch due to their NordLayer product and the promise of a s...
Read more
Aug 1, 2022
Microsoft recently made a big jump in the security of the Office suite by finally blocking macros by default! This is a fantastic step forward as macros have al...
Read more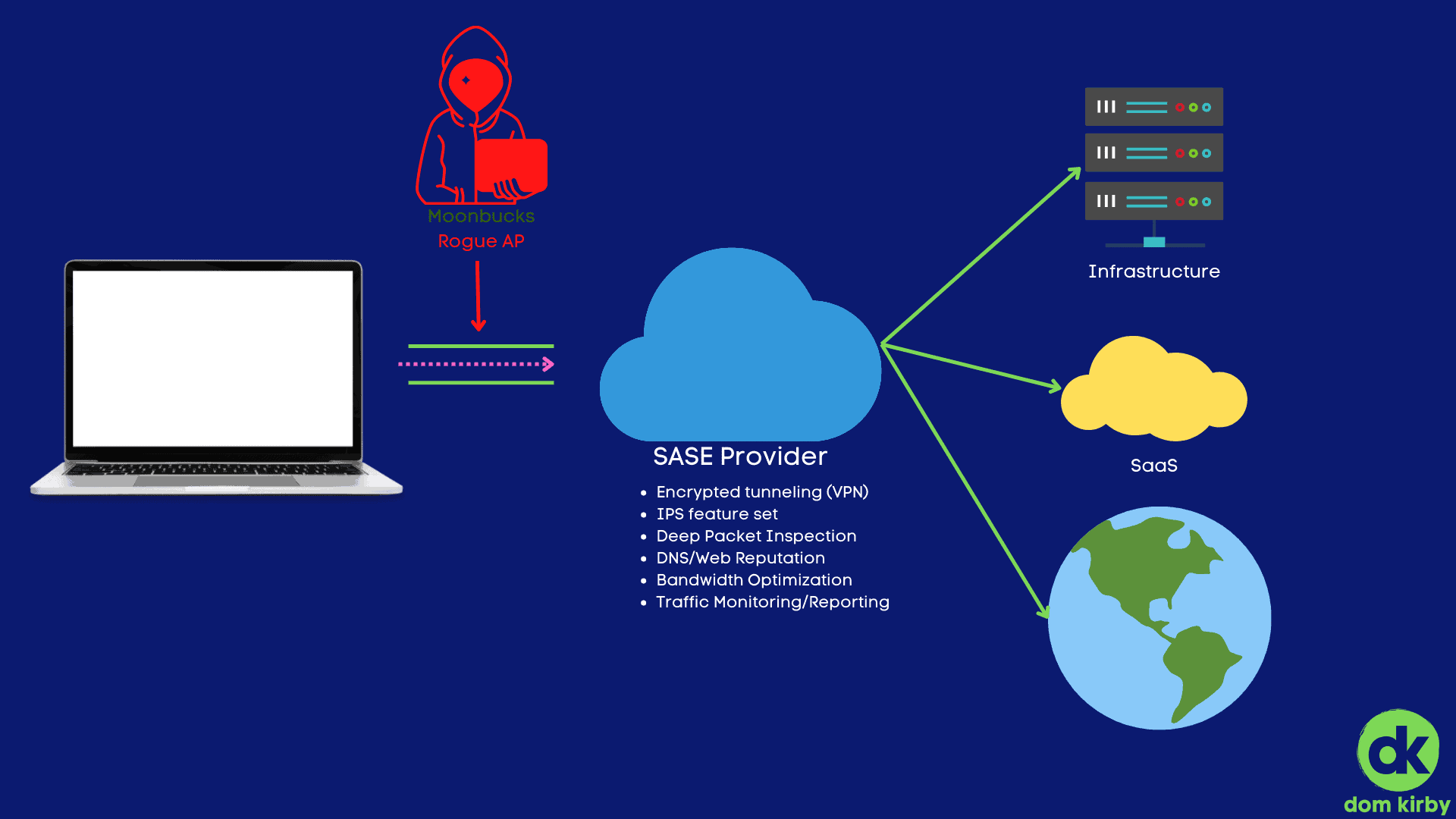
Jul 17, 2022
Now that the new normal is work from anywhere, we've got a major limitation on our hands: network protection. We can solve some of this with DNS filtering, whic...
Read more
Jun 26, 2022
It's not us, it's you. We need to talk about marketing and how we should be presenting our products and services to newer practitioners in our space. For too lo...
Read more
May 29, 2022
Back in January, I shared some ideas around how I'd personally approach NCE. To this day, it's one of my most popular posts. To that end, I thought I should ela...
Read more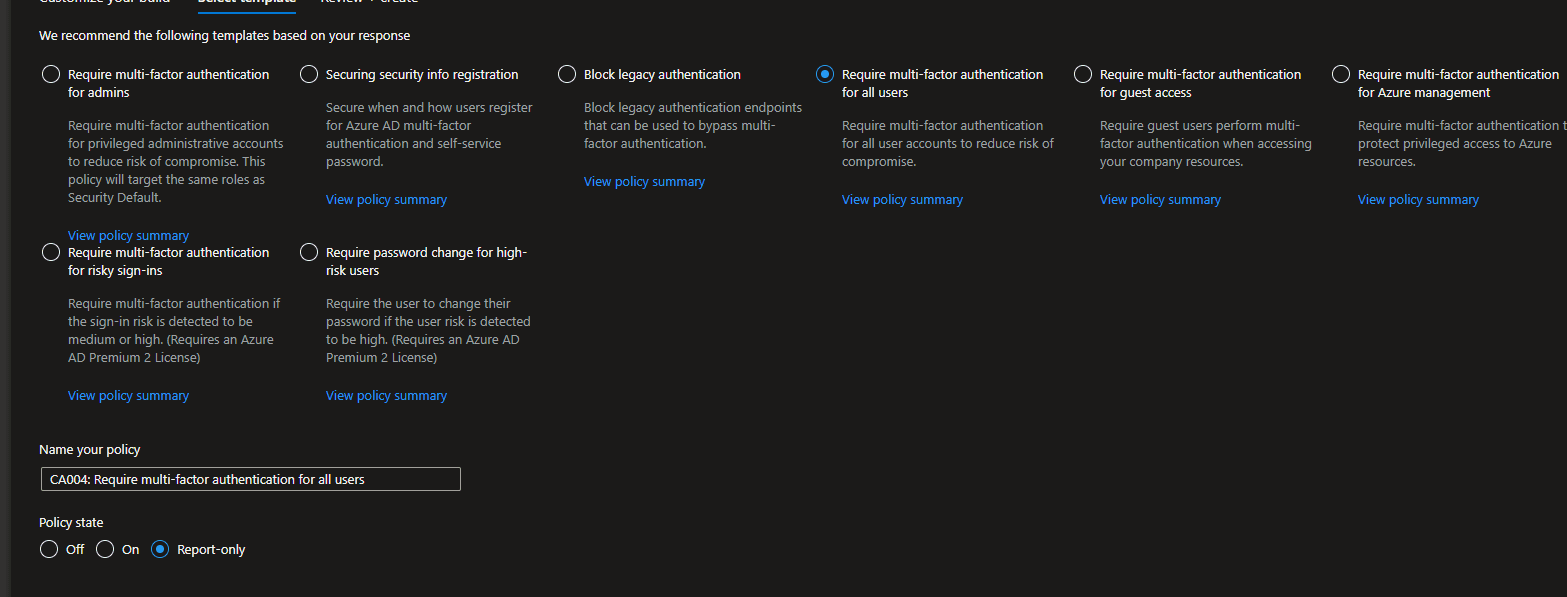
May 27, 2022
One of the bigger challenges with Conditional Access is baselining your security templates. As Microsoft so eloquently put it, Identity is the New Battleground,...
Read more
May 18, 2022
I never envisioned myself writing about these three companies agreeing, but here we are. And the news is fantastic. I've long been a proponent of passwordless a...
Read more
May 11, 2022
As a trusted technology provider and business advisor, your MSP has some serious horsepower. It's why Matt and I are constantly talking about the importance of ...
Read more
May 8, 2022
We live in a time where we can live a seamless technological life in our personal world. What do I mean? Should we choose to, we can tell our home goodnight and...
Read more
May 1, 2022
I was perusing one of my favorite cyber news spots, The Record, and stumbled on this article: Connecticut inches closer to becoming fifth state with data privac...
Read more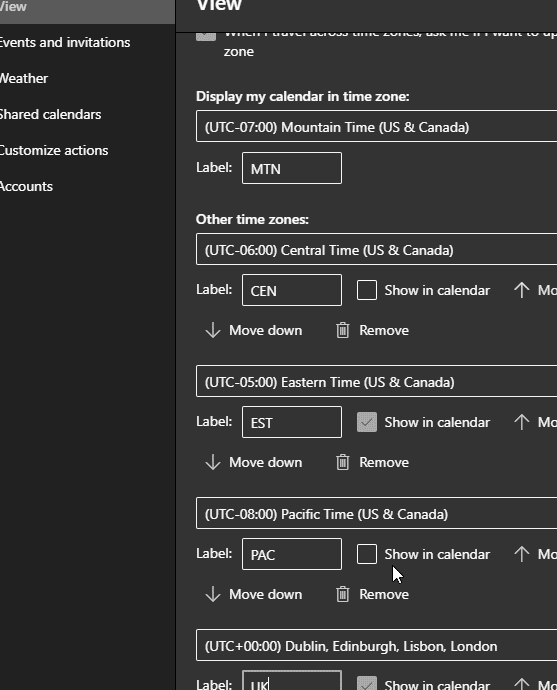
Apr 11, 2022
If you're anything like me, it's common for you to book calls with folks across time zones. I frequently find myself booking calls with folks all over the count...
Read more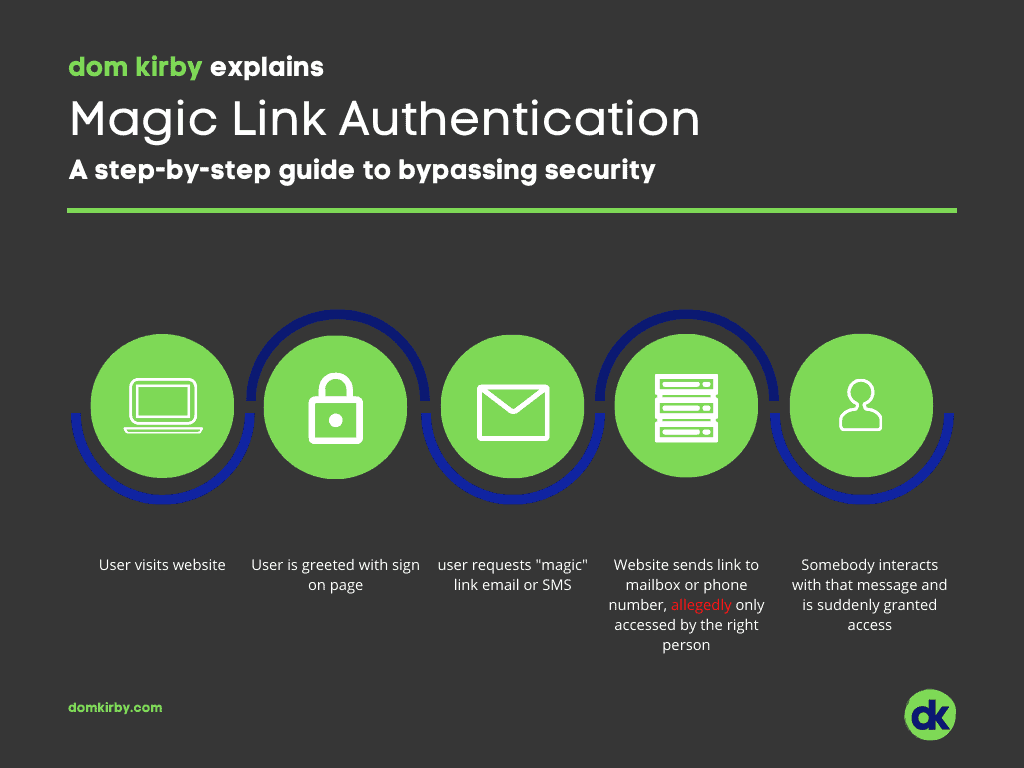
Apr 4, 2022
Click here to get a link to login. Magic links are suddenly everywhere, and I simply refuse to accept the logic behind them. Before I rant a bit about why you s...
Read more
Mar 29, 2022
We've all been there; in fact I feel like I'm there all the time. Imposter syndrome is real, in almost every industry. As we move up in our careers, tackle new ...
Read more
Feb 28, 2022
In a subtle update to the Microsoft Partner Security Requirements article on February 24th, Microsoft precludes the use of third-party MFA for partners wanting ...
Read more
Feb 28, 2022
As a cyber nerd, my first question when tensions went up in the region was 'what are the cyber implications?' The atrocities happening in Europe are shocking fo...
Read more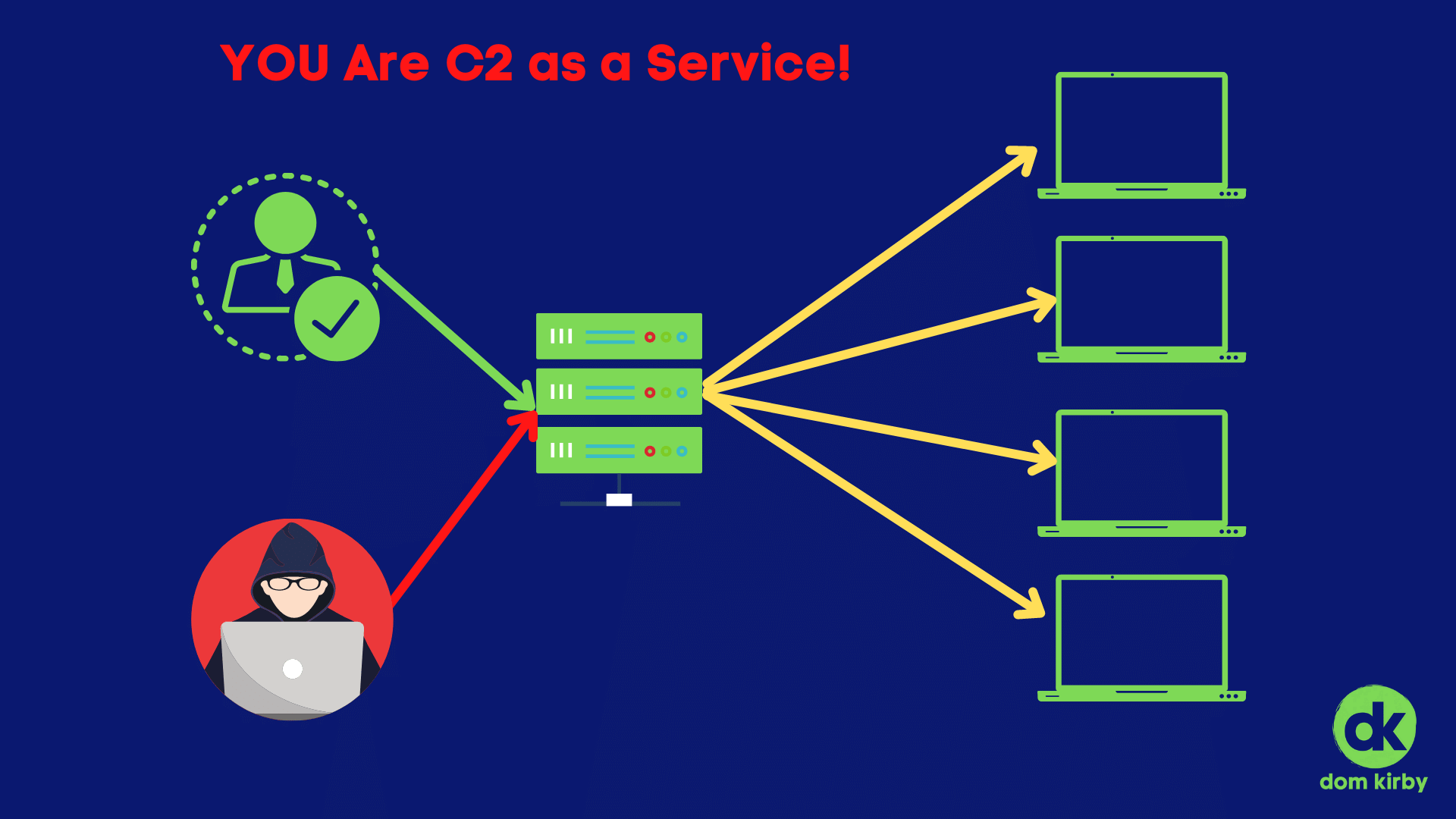
Feb 23, 2022
Threat actors are using your infrastructure for command and control as a service! When it first became a thing, remote controlling a computer was a thing of mag...
Read more
Feb 21, 2022
In my previous Baby Steps episode, we reviewed smart ways to implement data loss protection for every client. This episode focuses more so on outward protection...
Read more
Feb 18, 2022
My kids disappeared my wallet into the Twilight Zone that only kids have access to. We've turned the house upside down looking for it. If you're a parent, you e...
Read more
Feb 14, 2022
After my previous Modern Security Baby Step, I posted a poll on LinkedIn so that you could decide the next topic! Surprisingly, you voted on Data Loss Preventio...
Read more
Feb 11, 2022
Ahh texting. Arguably the start of the digital communications revolution. The good 'ol short message service (SMS). To this day, texting is a key method of comm...
Read more
Feb 10, 2022
The way people engage with brands has shifted monumentally in the last decade, even more so in the last 24-months. We engage with things on the internet, period...
Read more
Feb 8, 2022
I've decided to write a small series of posts focused on modern security. That is, security in the modern workplace environment. You see, the way we need to thi...
Read more
Feb 6, 2022
I might generate a bit of a stir, but this must be said! > You cannot be defensible if you are not meaningfully implementing multi-factor authentication. If I'm...
Read more
Feb 4, 2022
Microsoft is one of the most powerful, intelligent cybersecurity firms on the planet. Many people don't realize just how much intelligence Microsoft has at thei...
Read more
Feb 1, 2022
Technology serves business, not the other way around. Technology and the services around it aren't (or shouldn't be) commodities. For too long, we've been commo...
Read more
Jan 28, 2022
Microsoft's New Commerce Experience (NCE) comes with substantial changes to the way we're used to doing business with Microsoft. From price increases to extra p...
Read more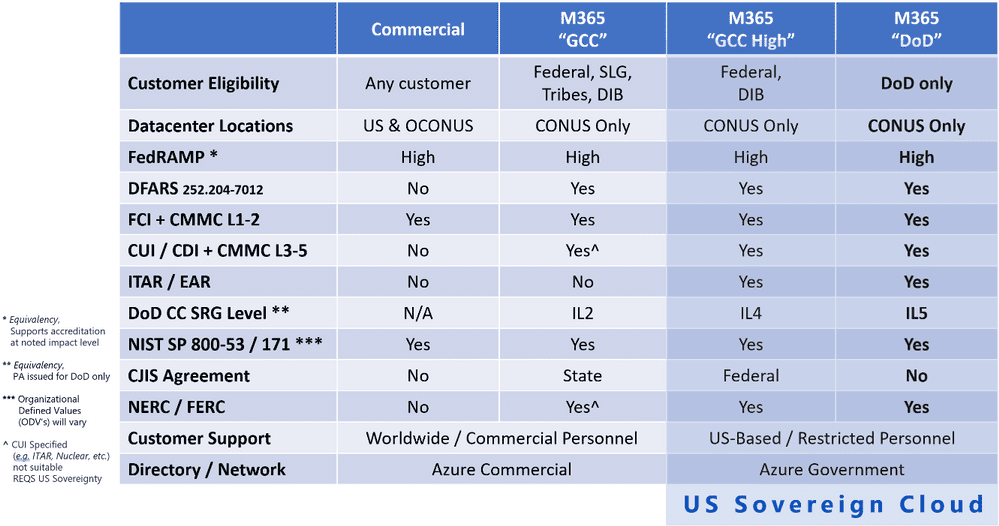
Jan 26, 2022
Disclaimer: This article is based on my own opinions from reading Understanding Compliance Between Commercial, Government and DoD Offerings and should not be ta...
Read more
Jan 24, 2022
\[et\pb\section fb\built="1" admin\label="section" \builder\version="3.22" global\colors\info="{}"\]\[et\pb\row admin\label="row" \builder\version="3.25" backgr...
Read more
Jan 23, 2022
Frameworks are extremely important in the modern security landscape. With the level of complexity of today's average environment, even in the SMB arena, shootin...
Read more
Jan 22, 2022
Ransomware, zero-days, and other "sexier" attacks have dominated the news lately. But an article I read on The Record served as an important reminder that busin...
Read more
Jan 19, 2022
We’re finally getting to the point of seeing more successful law enforcement activity against cybercrime groups. From the FSB arresting the REvil gang to the ta...
Read more
Jan 16, 2022
\[et\pb\section fb\built="1" admin\label="section" \builder\version="3.22" global\colors\info="{}"\]\[et\pb\row admin\label="row" \builder\version="3.25" backgr...
Read more
Jan 12, 2022
Did you know that Windows 11 ships with built in support for DNS over HTTPS (DoH)? DoH is both a privacy and security enhancement that allows you to encrypt you...
Read more
Jan 12, 2022
So, on my phone, I use Microsoft Start as a news feed. I know, ANOTHER Microsoft product, Dom? Yes, maybe I have a problem, but I like how it customizes my feed...
Read more
Jan 10, 2022
As the “tech expert in the family,” I get this question a lot. I figured that I may as well answer it for whoever in my audience would listen. In this article, ...
Read more
Jan 6, 2022
THE RECORD 5JAN22 - The New York Attorney General announced Wednesday that it discovered over 1.1 million compromised online accounts resulting from an investig...
Read more
Jan 5, 2022
Via The Record 5JAN22 - The Federal Trade Commission made an announcement on Tuesday that it may pursue legal punitive action against entities who experience a ...
Read more