I recently came across an article stating that ransomware attacks targeting healthcare organizations surged following the Change Healthcare incident. For a quick recap, the Change Healthcare attack crippled the filling of prescriptions and other healthcare operations...
Category: Cybersecurity
Data Loss Prevention for Any SMB
It's time for a new guide for MSPs! The Safeguards within CIS Control 3 speak to the need for proper Data Protection. Implementation Group 1 (i.e.: the minimum we should do) covers some basic data management and protection practices such as: Establishing and...
CISA’s Secure by Design Pledge
In some very exciting news today, CISA announced their Secure by Design Pledge. The Secure by Design Pledge is a voluntary commitment that was signed by 68 software companies, committing to design their products from the ground up in a more secure way. I've linked the...
Are Passkeys the Answer to Passwordless Adoption?
In our digital age, the concept of living in a passwordless world is eagerly anticipated. It's common knowledge that passwords are a hassle – users struggle to create and remember strong passwords, and the tools meant to help, like password managers, haven't gained...
Tips for a Successful MFA Rollout
IMPORTANT NOTE: I'm trying something new here and looking for feedback (on LinkedIn). I've written this post using Microsoft Copilot by creating a general outline of "points to hit" in addition to a key topic. I'm experimenting with this to see if it can expand my...
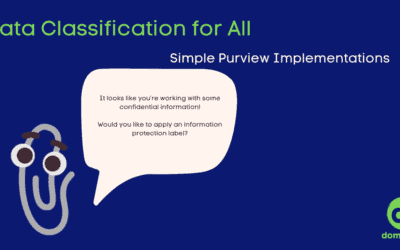
Data Classification for All
I figured I would expand on my Purview Information Protection information by creating a general guide around information protection labels. In this guide, I take a deeper dive into Purview Information Protection and provide you with some implementation examples that...
Traffic Light Protocol with Purview Information Protection
I recently made a post on LinkedIn about how I've applied the Traffic Light Protocol within my own Microsoft 365 tenant using Purview Information Protection. I opted for this route because, in my personal tenant, I'm not often collaborating with other members of the...
Empowering Tomorrow’s Cyber Practitioners
In my last post, I wrote about the idea that cybersecurity doesn’t need colleges. For this post, I wanted to shed some light on how I think we can build a modernized cybersecurity pipeline that prepares practitioners for the reality of working in this space. With the...