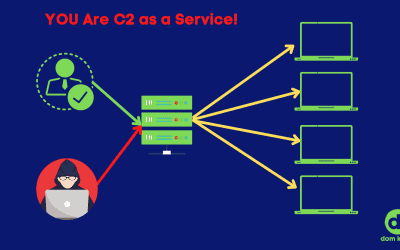
Threat actors are using your infrastructure for command and control as a service! When it first became a thing, remote controlling a computer was a thing of magic. So much "how are you doing this?!" Threat actors have caught onto this. Creating one convenient place to...
It’s Time: Drop Persistent Remote Access
read more